Before I start discuss about the difference, just want to share what these tools are used for and why we need to know the difference
DirSync, Azure AD Sync and Azure AD Connect are used to sync on-premises Active Directory to cloud based directory service like Azure AD instance, Office 365, Dynamics Online and other Microsoft Cloud Services
Reed Also: Active Directory on Cloud
All are used for Single Sign-On (SSO) and user can use the a single user account and password to access there cloud based application on Office 365, Dynamics Online and Azure AD, we can synchronize user account and there passwords
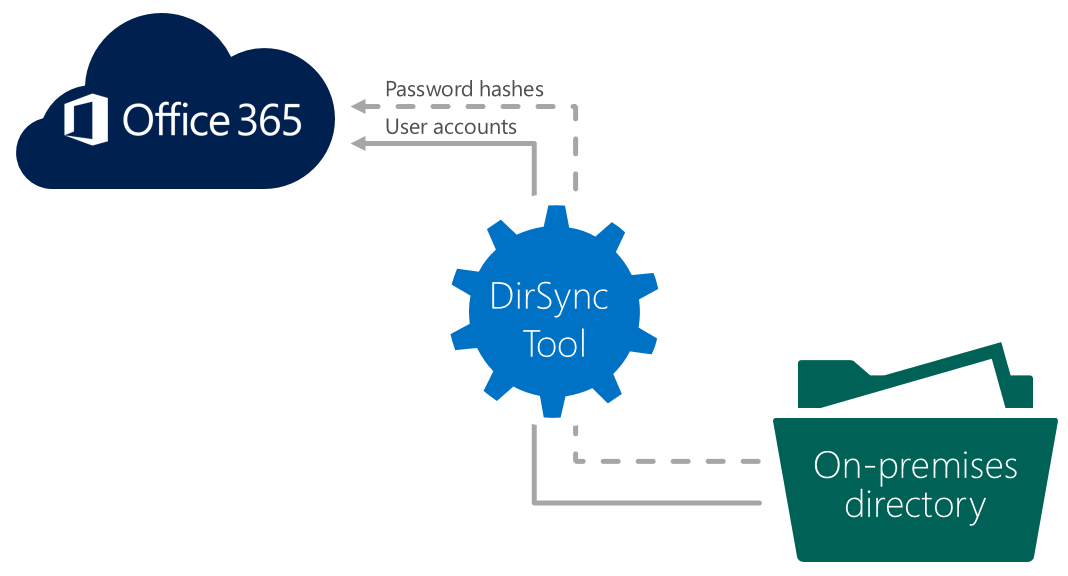
DirSync
DirSync to sync your local on-premises Active Directory with cloud based services. dirsync is the easiest option to implement however it comes with less flexibility what you can change in the configuration and It doesn’t support multi-forest environments.
Azure AD Sync
Azure AD Sync is advance version of DirSync, it support most of the functions of traditional DirSync, and adds extra functionality such as mutli-forest support and password write back. I recommend to use the Azure AD Sync tool because it’s more flexible then Dir Sync
Azure AD Connect
Azure AD Connect is currently in Preview stage. It has many of the same features as DirSync and Azure AD Sync, its going to replace DirSync and Azure AD Sync and it has plans for many other features such as non-AD LDAP support.
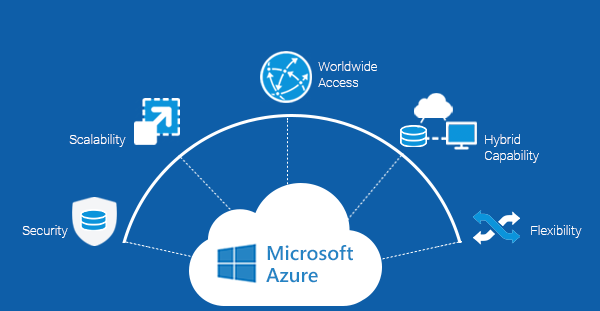
Azure Connect is recommended for larger organizations that have greater flexibility requirements, it provides consistent experience in hybrid environments that may or may not entirely utilize Microsoft on premise solutions
Why use Azure AD Connect?
Integrating on-premises directory service with Azure AD makes your users more productive by providing a common identity for accessing both cloud based and on-premises service and application.
I think of below advantages by providing common identity for users in an any organizations:
Companies can provide users with a common hybrid identity across on-premises or cloud-based services with Windows Active Directory and then connecting to Azure Active Directory.
Administrators can use multi-factor authentication to provide conditional access based on application, device and user identity, network location and many more
Users can use their user accounts in Azure AD to access Office 365, Microsoft Intune, SaaS apps and any other third-party applications.
Application can be developed with common identity model, integrating applications into Active Directory on-premises or Azure for cloud-based applications